Microsoft Office 365 Advanced Threat Protection: Complete Overview
Nowadays, there are countless threats that can lead to a security breach and subsequent data loss. In 2021, spam and phishing emails were the most common delivery method leading to ransomware infections. Trying to detect and deter malicious attacks manually is an impossible task. However, for Office 365 applications and services, Microsoft offers a suite of detection and response tools to automate and simplify security.
Office 365 Advanced Threat Protection (ATP), which since September 2020 has become Microsoft Defender for Office 365, is a collection of tools dedicated to preventing online threats. The different policies and rules allow you to protect on-premises and cloud environments by filtering incoming and outgoing communication and verifying other shared content.
What Is Advanced Threat Protection?
Office 365 Advanced Threat Protection (ATP) is a cloud-based filtering service for cyberthreat prevention and detection. ATP can protect your organization against viruses and other malware, including zero-day attacks, that are disseminated via Office 365 services. ATP can recognize the newest viruses and unidentified complex threats that have not yet been studied and cannot be recognized even by most antiviruses with the latest virus signature databases.
How Office 365 Advanced Threat Protection Works
Office 365 Advanced Threat Protection relies on policies that should be configured by a system administrator. ATP filters data, suspicious behavior, and other parameters at the level of an organization, domain, user, and recipient.
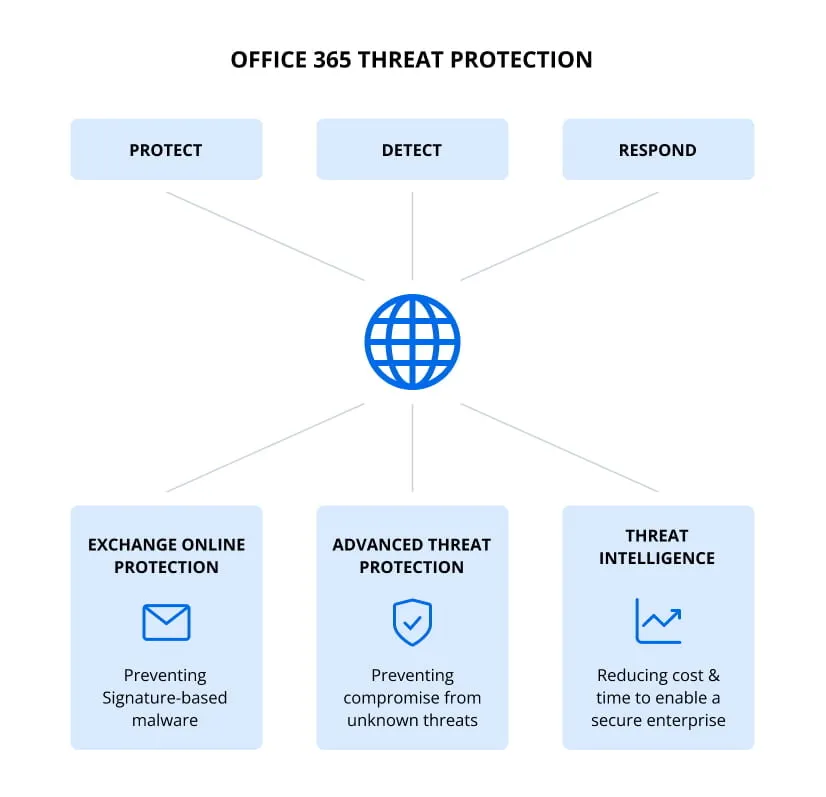
Office 365 Advanced Threat Protection can work in integration with Exchange Online Protection (EOP) and Office 365 Threat Intelligence. Using ATP in the cloud can offload your mail servers and protection systems on the mail servers, including on-premises servers. It is not recommended that you turn off Office 365 Advanced Threat Protection even if you use other tools like EOP.
Advanced Threat Protection can protect email attachments, links, and files uploaded by users to OneDrive for Business, SharePoint Online, and Teams. In addition, ATP can detect links to phishing websites, sites with uploaded malware code, and the presence of malicious code in downloaded/uploaded files. URL trace capabilities can help you block potential sources of threats and understand their nature and where they are coming from.
Advanced Threat Protection Features
Office 365 Advanced Threat Protection contains many useful features to protect your data when using Office 365 services. Let’s explore these features in detail.
Policies
Policies determine the protection level and the response to predefined threats, both of which can be set on different levels. Policies provide flexible options, which a system administrator managing Microsoft 365 can configure. As a system administrator, you can set who is affected by policies and how strict these policies are.
Safe attachments
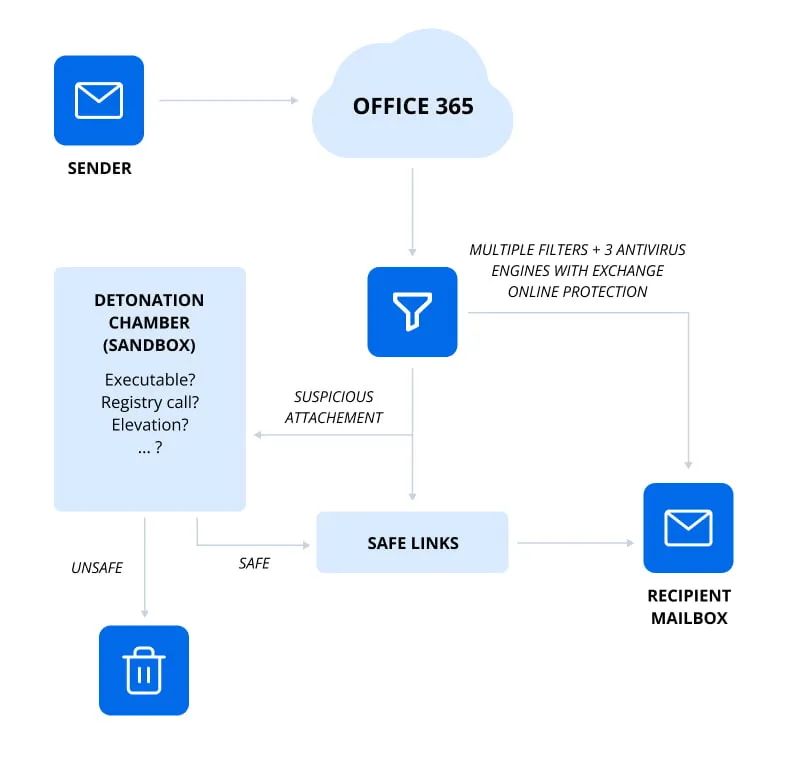
Safe attachments ensure that files attached to email messages are not malicious. Zero-day protection is provided to safeguard your email messaging system. Before a message is received in a user’s mailbox, the message is routed to a special environment, where attachment files are checked by using virus signatures, machine learning, and advanced analysis techniques to detect viruses. If no viruses are detected in the email attachment, the email message is forwarded to a mailbox. The feature responsible for safe attachments is called attachment sandboxing.
Safe Links
Safe Links use a working principle similar to safe attachments. This feature checks links in emails and other files that are uploaded/downloaded in the Microsoft 365 environment. If Microsoft 365 ATP detects that a link is not safe, a warning message is displayed (just like for downloadable files).
You can configure the feature to redirect users to a warning page if a user tries to click a link detected as malicious. The system dynamically blocks malicious links. The Safe Links feature was updated and now doesn’t substitute the original link with a modified link to a web page in the Microsoft cloud.
ATP for SharePoint Online
ATP for SharePoint Online protects users who collaborate by using SharePoint Online sites and shared files inside your organization. This feature detects and blocks suspicious files in document libraries and team sites, including files stored on OneDrive. The identified malicious content is blocked. Users cannot open, copy, move, edit, or share a blocked file that is classified as malicious. The malicious file can only be deleted. The ability to download the file depends on the configuration.
Anti-phishing protection
After defining anti-phishing policies, self-learning system models with complex algorithms are used to detect phishing attacks automatically and quickly. Mailbox intelligence analyzes user email and communication habits and aggregates the data to help detect phishing attempts in the future. These tough measures make any scamming attack difficult to accomplish.
Quarantine
Unwanted and potentially dangerous files can be moved to quarantine. As a system administrator, you can manually restore or delete the quarantined data. Otherwise, this data is deleted after the configured retention period expires. You may be familiar with the working principle of quarantine if you have used Microsoft 365 Exchange Online Protection.
Spoof Intelligence
Hackers can send emails on behalf of one or more accounts by substituting the sender’s name. When a user receives such a “spoofed” email, it may appear safe if the sender uses a manager’s name in the sender field. A spoofed email, which can contain a call to transfer money, send credentials, or malicious scripts, is not safe and constitutes a threat to users and the whole organization.
Office 365 Advanced Threat Protection includes the Spoof Intelligence feature that can detect whether a sender is using a real name or a spoofed name. You can see the complete list of users who use a particular company domain and review who is spoofing your organization’s domain or any external domains. As an administrator, you can block the sender using a domain name or user name pretending to be an employee at your organization.
Reports
Office 365 Advanced Threat Protection provides informative reports so you can see the protection status and analyze incoming threats. A report is a single view, which combines information about detected threats, including malicious email and other malicious content. Threats detected by Office 365 Advanced Threat Protection and Exchange Online Protection are shown in the reports. Information for the previous 90 days (the maximum period that can be configured) is displayed in the reports. After analyzing the reports, you can adjust the policies.
Threat Investigation and Response
If you work in a large company with many Office 365 users, you may be overwhelmed with a large number of security alerts to deal with. Sorting a high number of emails based on the attributes is a time-consuming task. Office 365 Threat Investigation and Response can help system administrators and security specialists operate more efficiently. You can view detected threats and configure automated actions to mitigate different types of threats. You can compose playbooks with the appropriate actions for detected threats, as well as review and approve actions or recommendations suggested by Office 365 Advanced Threat Protection after an automated investigation to remediate threats.
Microsoft 365 Licensing
Unlike Exchange Online Protection, which is available by default for Microsoft 365 users, Advanced Threat Protection is available for top subscription plans or can be bought separately. For example, even Microsoft 365 E3 does not include advanced threat protection.
Microsoft Office 365 Advanced Threat Protection is included in the following subscription plans:
- Microsoft 365 E5
- Microsoft 365 A5
- Microsoft 365 Business Premium
However, you can buy the Office 365 Advanced Threat Protection license on top of the following subscription plans:
- Exchange Online Plan 1
- Exchange Online Plan 2
- Exchange Online Kiosk
- Exchange Online Protection
- Microsoft 365 Business Basic
- Microsoft 365 Business Standard
- Microsoft 365 Enterprise E1
- Microsoft 365 Enterprise E3
- Microsoft 365 Enterprise F3
- Microsoft 365 A1
- Microsoft 365 A3
If Office 365 Advanced Threat Protection is not included in your subscription plan, you can purchase one of the standalone ATP subscription plans using a per-user licensing model:
- Advanced Threat Protection Plan 1
- Advanced Threat Protection Plan 2
Advanced Threat Protection Configuration
Update: Office 365 Advanced Threat Protection became Microsoft Defender for Office 365 in September 2020. Now, to configure any of the features listed below, you need to access the Defender Portal.
Let’s look at how to configure Office 365 Advanced Threat Protection:
- Open the web interface of the Microsoft 365 admin center by using the link https://admin.microsoft.com and go to
Admin Centers > Securityin the left pane of the window.
As an alternative, you can open a direct link to the Microsoft 365 Security & Compliance admin center: https://protection.office.com
- In the left pane, click
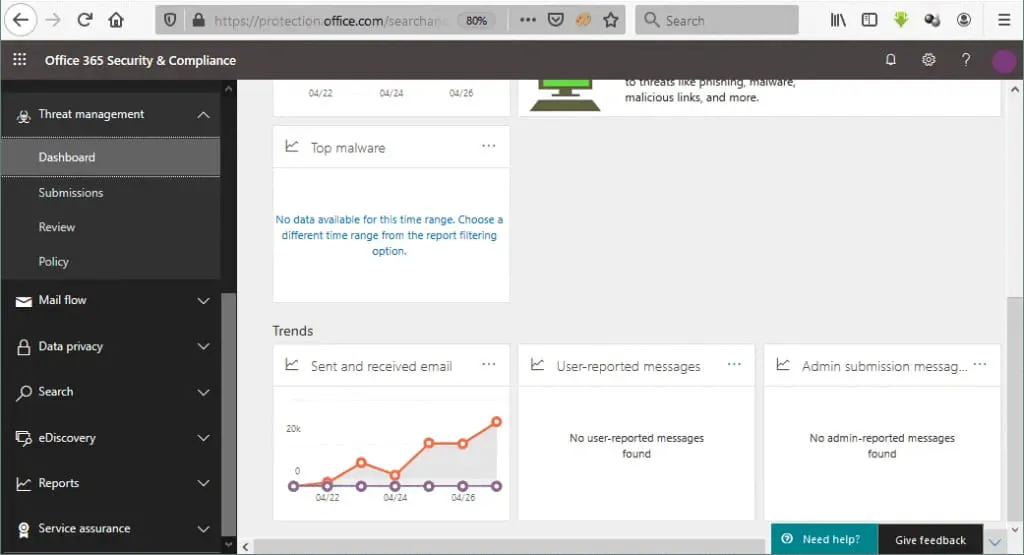
Threat managerand then clickDashboard.
The security dashboard, also referred to as the threat dashboard, displays the current threat protection status and links to configuration pages.
Anti-malware policies
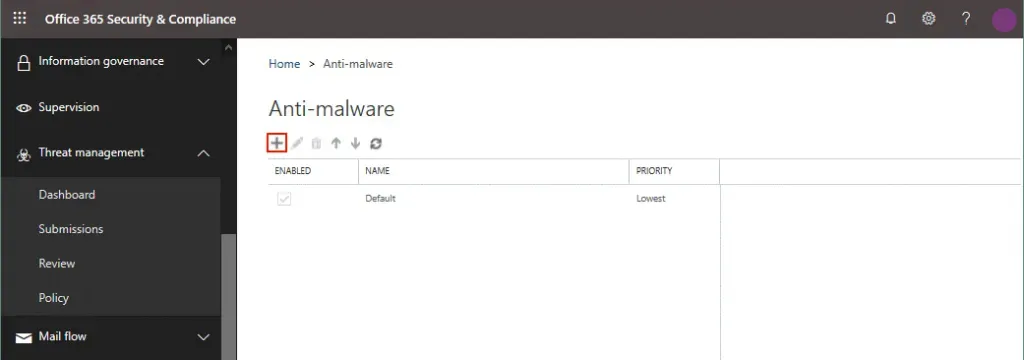
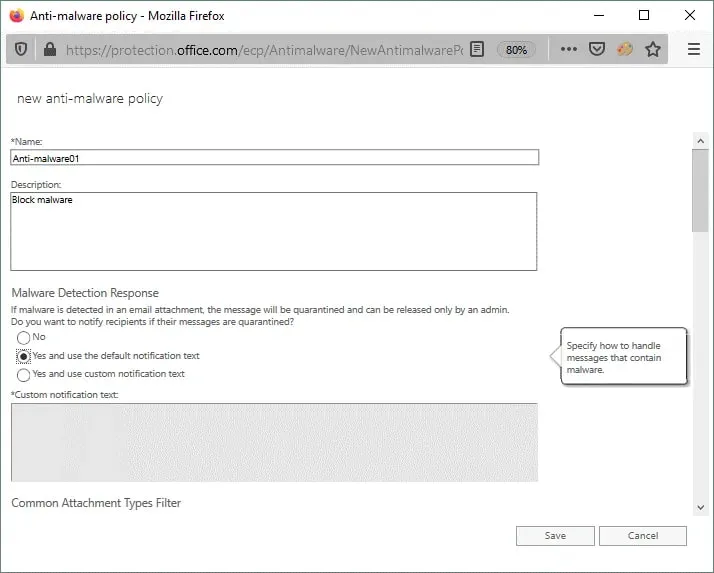
Click Policy in the left pane, or the navigation pane, and the page where you can view, edit, and create policies appears. You can configure anti-phishing, anti-spam, and anti-malware policies. Let’s look at how to create a new anti-malware policy:
- Click
Anti-malware.
- On the anti-malware page that opens, click the
+icon to create a new anti-malware policy for Office 365 Advanced Threat Protection.
- A new pop-up window opens.
Enter the policy name and description, and define other policy options such as:
- Malware detection response
- Common Attachment Types Filter
- Malware Zero-hour Auto Purge
- Notifications
Finally, specify to whom this policy applies, and hit Save.
The policy is now created and displayed in the list of policies on the Malware page.
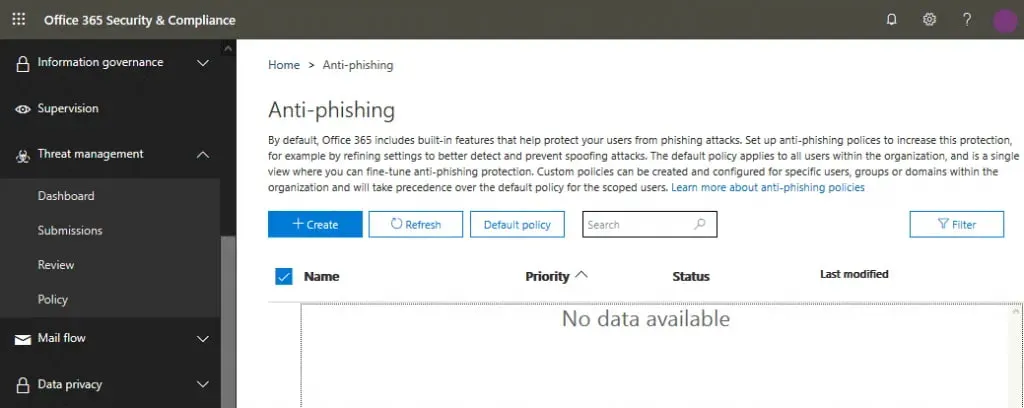
Anti-phishing policies
Anti-phishing policies are created slightly differently from anti-malware-policies:
- Go to Threat Management > Policy and hit
Anti-phishing.
The Anti-phishing page opens. If you’re opening this page for the first time, the list of anti-phishing policies will be empty.
- Click the
+Createbutton to create a new anti-phishing policy for Office 365 Advanced Threat Protection.
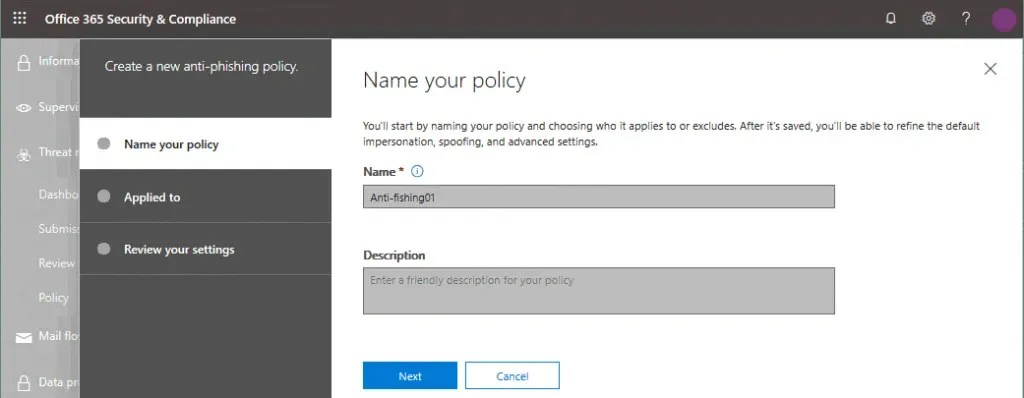
- A new policy wizard opens as a pop-up window. Complete all the steps in the wizard:
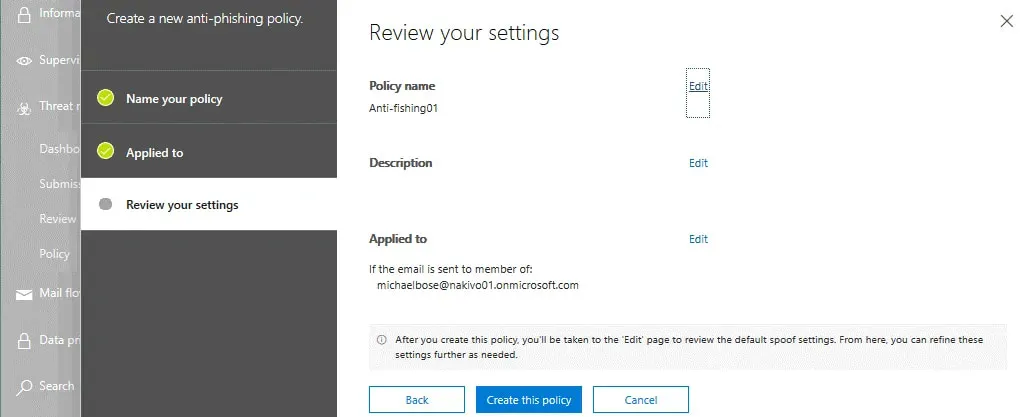
Name your policy. Enter a name for a new anti-phishing policy. You can also enter a description.
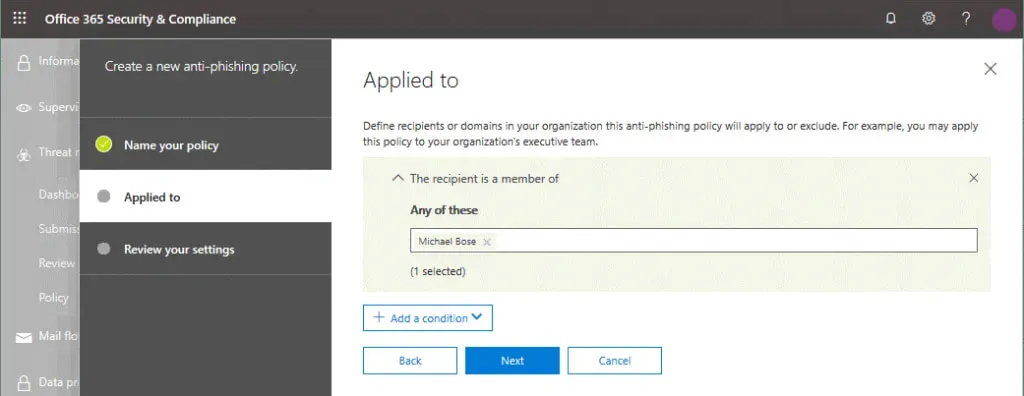
Applied to.Define the recipients or domains in your organization to which this policy will apply or exclude by adding conditions and selecting recipients. For example, you can apply the policy to an entire domain, group membership, or group and domain combinations. Then hitNext.
Review your settings.Check your settings and edit them if needed. If everything is correct, hitCreate this policy.
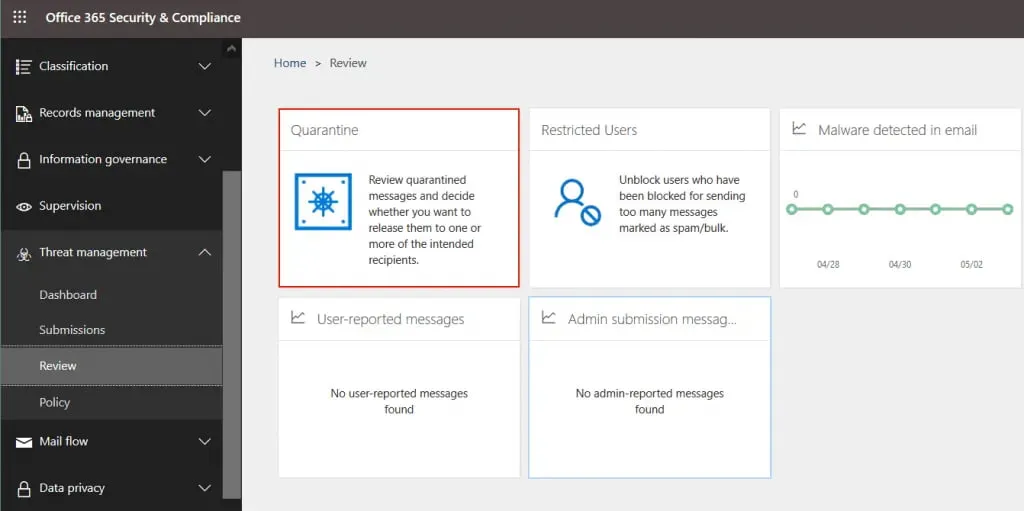
Quarantine
Email messages and files that are classified as potentially dangerous are moved to quarantine if the appropriate settings are used for Office 365 Advanced Threat Protection. Go to Treat management > Review > Quarantine to open quarantine. You can also use this direct link: https://protection.office.com/quarantine
Note: Quarantine can be accessed by the administrator or another user who has permissions to manage quarantine. Members of the Quarantine role in the Office 365 Security & Compliance Center have permissions to manage quarantine.
On the Quarantine page, you can sort results by clicking the title of the needed column. Click Modify Columns to select which columns must be displayed.
Reports
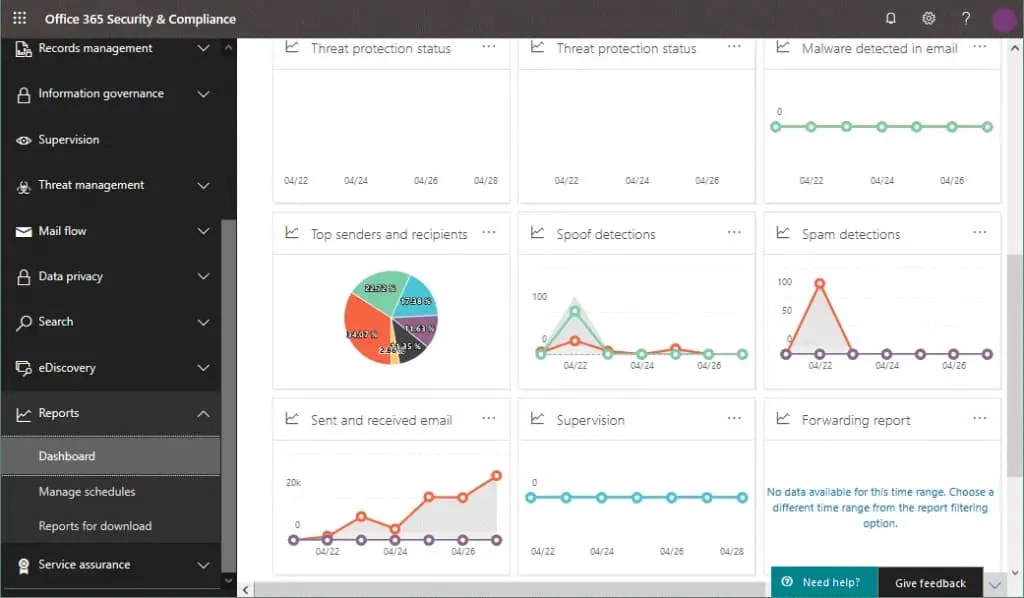
Reports are useful for viewing the current status and statistics of your Microsoft 365 environment. In the navigation pane of the Office 365 Security & Compliance admin center, click Reports > Dashboard to see the dashboard with graphs and diagrams.
On this page you can see the summary including:
- Recent reports for download
- Top 5 labels
- Labels trend over the past 90 days
- How labels were applied
- Labels classified as records
- Exchange Transport Rule
- Threat protection status
- Malware detected in email
- Top malware
- Top senders and recipients
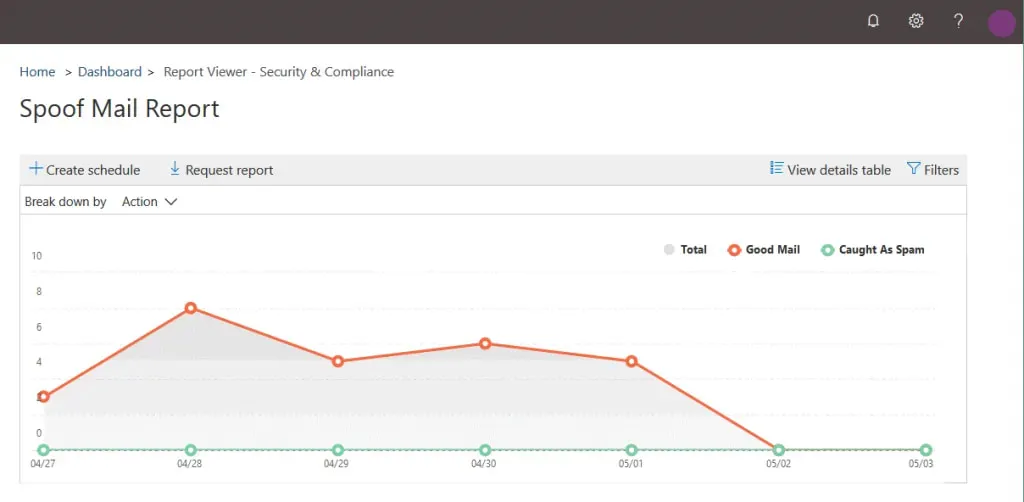
- Spoof detections
- Spam detections
- Compromised users
- Sent and received email
- Supervision
- Forwarding report
- Connector report
- Encryption report
Hover over the graph to see more information. Click the needed chart or diagram to open it in full-window mode and see the details. After clicking Spoof detections, a detailed spoof mail report is displayed.
By default, a 7-day period is displayed on the charts and graphs, but this period can be increased up to 90 days in the settings. Trial users of Microsoft 365 with Advanced Threat Protection can view data for a maximum of 30 days in reports.
Conclusion
Office 365 Advanced Threat Protection is integrated with other Microsoft 365 services such as OneDrive, SharePoint Online, Exchange Online, SharePoint Online, and other services. ATP helps you protect your emails from various security threats like harmful links, viruses and malware.
However, to achieve a higher level of data protection, you should back up all your Microsoft Office 365 data with a dedicated solution like NAKIVO Backup & Replication. The NAKIVO solution allows you to create incremental backups of Microsoft 365 data and offers flexible point-in-time restores.