Types of Network Topology Explained
When building a computer network, you need to define which network topology you want to use. There are multiple types of network topologies used nowadays, each with its pros and cons. The topology you choose determines the optimal performance of your network, scalability options, ease of maintenance, and the costs of building the network. That’s why it is important to select the right network topology type.
This blog post covers types of network topology, their advantages, and their disadvantages. It also provides recommendations on which network topology to use in different scenarios. Practical examples of using a specific type of network topologies can help you understand when each topology can be applied.
What is Network Topology?
The network topology or network configuration defines the structure of the network and how network components are connected. Network topology types are usually represented with network topology diagrams for convenience and clarity. There are two types of network topology: physical and logical.
Physical topology describes how network devices (called computers, stations, or nodes) are physically connected in a computer network. The geometric scheme, connections, interconnections, device location, the number of used network adapters, types of network adapters, the type of cable, cable connectors, and other network equipment are the aspects of the physical network topology.
Logical topology represents the data flow from one station to another, how the data is transmitted and received, the path of data in the network, and which protocols are used. The logical network topology explains how data is transferred over a physical topology. Cloud and virtual network resources are part of the logical topology.
Point-to-Point Network Topology
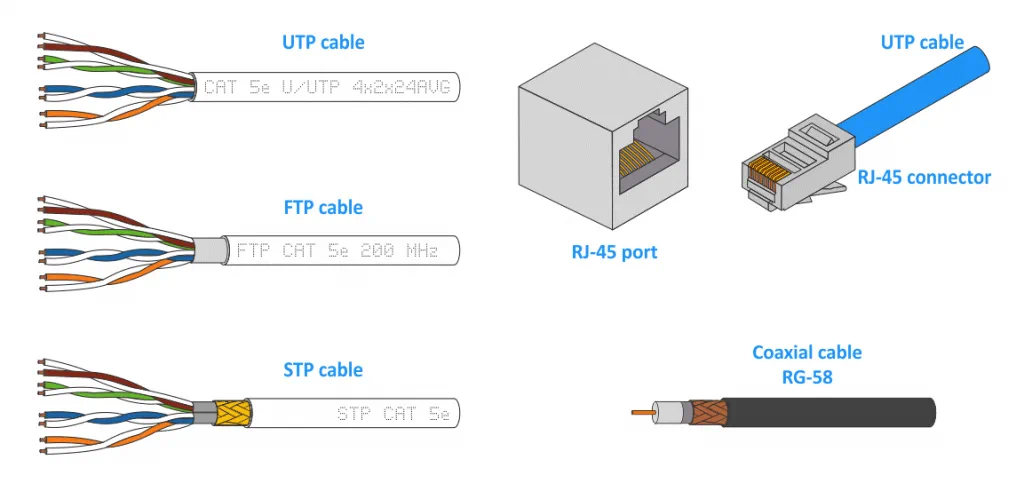
Point-to-point network topology is the simplest network topology used when only two computers or other network devices are connected to each other. A single piece of cable is used in this case. The most common example of the point-to-point network topology is connecting two computers (that have Ethernet network adapters with RJ-45 ports) with a twisted pair cable (UTP Cat 5e, FTP Cat 5e, STP Cat 5e, etc.). The point-to-point type of topologies is also called the P2P topology.
Refer to the last section of the blog post to learn about the different Types of Cables.
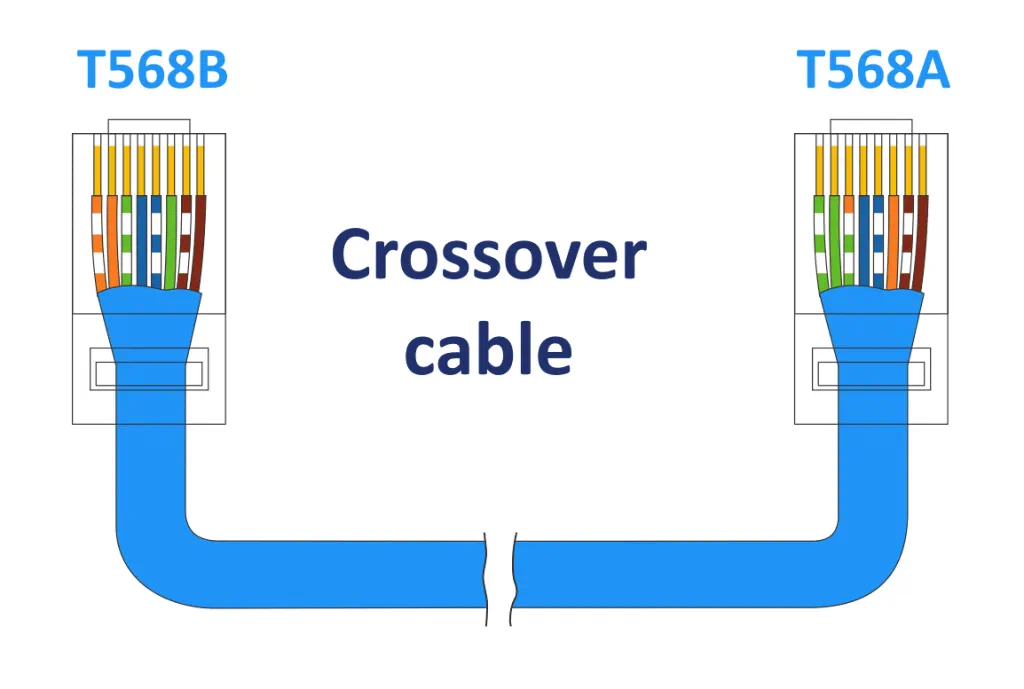
Ethernet crossover cable of category 5e is a cable that has four twisted pairs of wires. The cable has RJ-45 connectors on both ends, with T568A wiring on one end of the cable and T568B on the other end. The crossover cable is used to connect network devices of the same type, such as two Ethernet cards of different computers. Modern network cards can work with a patch cable without a crossover cable when connecting two computers using the point-to-point network topology. The connection is possible thanks to Ethernet Auto MDI-X support (medium dependent interface crossover).
Patch cords or patch cables are used to connect a network card of a computer to a switch and to connect switches to each other. Both ends of a patch cord are crimped by using the T568B standard (T568A also can be used for both ends of the patch cord, but this practice is not common).
Bus Network Topology
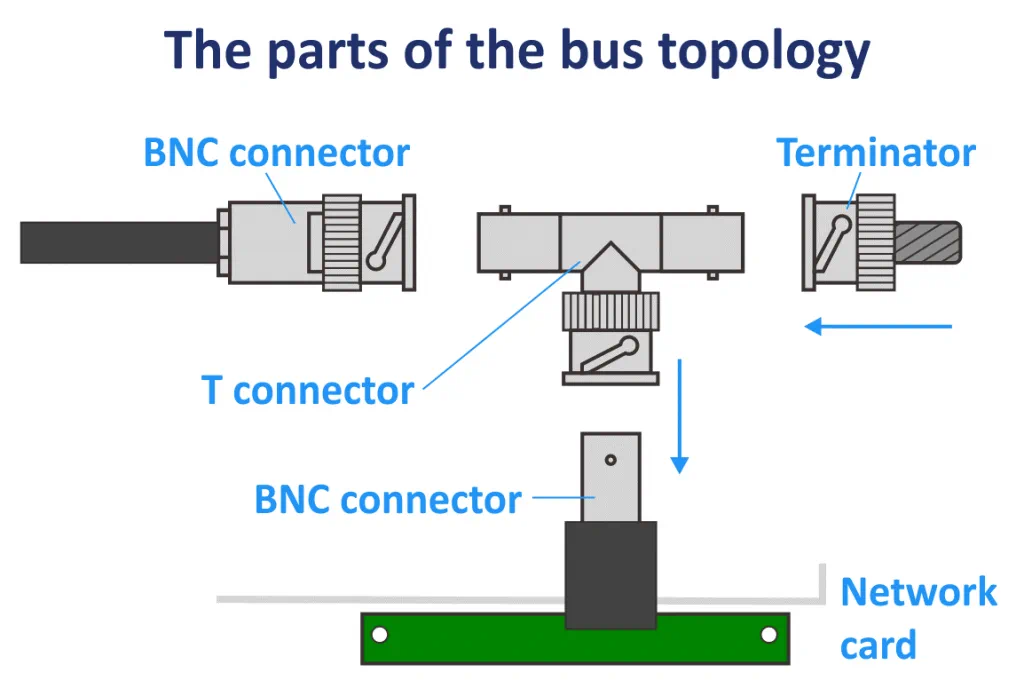
In a bus topology, the main cable is called a common cable or a backbone cable. The stations are connected to this main cable by using other cables that are called drop lines. The tap device is used to connect drop lines to the main cable. An RG-58 coaxial cable with an impedance of around 50-52 Ohms is usually used to build the network in a bus topology. BNC (Bayonet Neill-Concelman) connectors are used to connect parts of the network and connect a cable to the network card. Terminators are devices installed on each end of the backbone cable to adsorb signals and avoid reflecting the signals back to the bus (reflecting signals back causes serious issues in the network).
The installation difficulty of the bus topology is medium. The topology requires fewer cables than other types of network topology and costs less. This network topology is used for small networks. Scalability is low because the length of the backbone cable is limited and so is the number of stations that can be connected to the backbone cable. Every network device is connected to a single cable.
A bus topology makes detecting network failures difficult. If the main cable is corrupted, the network goes down. Every additional node slows down the speed of data transmission in the network. Data can be sent only in one direction and is half-duplex. When one station sends a packet to a target station, the packet is sent to all stations (broadcast communication). However, only the target station receives the packet (after verifying the destination MAC address in the data frame). This working principle causes network overload and is not rational. The network of the bus network topology type works in half-duplex mode.
The half-duplex mode does not allow stations in the network to transmit and receive data at the same time. The whole channel bandwidth is used when data is transferred in either direction. When one station is sending data, other stations can only receive data.
In the full-duplex mode, both stations can transmit and receive data simultaneously. The link capacity is shared between signals going in one direction and signals going in another direction. The link must have two separate physical paths to send and receive data. As an alternative, the entire capacity can be divided between signals going in both directions.
10BASE2 is part of the IEEE 802.3 specifications used for Ethernet networks with coaxial cable. The maximum cable length ranges between 185 and 200 meters. The maximum length of thick coaxial cable for the 10BASE5 standard is 200 meters.
CSMA/CD (Carrier Sense Multiple Access/Collision Detection) is the technology used to prevent collisions (when two or more devices transmit data at the same time and this leads to corruption of the transmitted data) in the network. This protocol decides which station in what moment can transmit data. IEEE 802.3 is the standard that defines LAN (local area network) access methods using the CSMA/CD protocol.
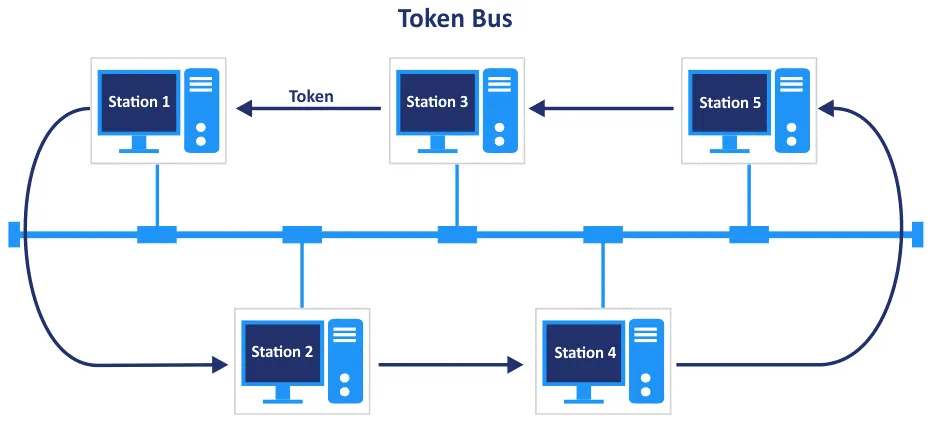
Token Bus
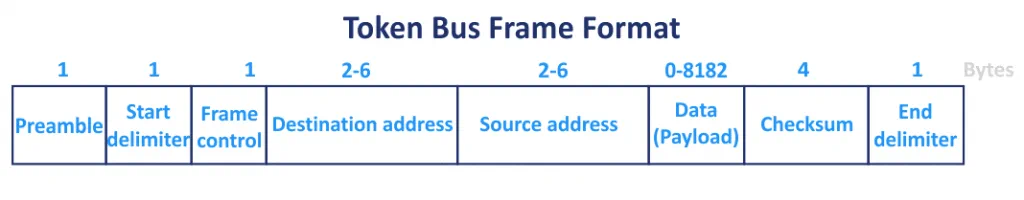
IEEE 802.4 is the Token Bus standard that is used to create a logical token ring in networks built using the bus topology. A token is passed from one station to another in a defined sequence that represents the logical ring in the clockwise or counter-clockwise direction. On the following image, for Station 3, the neighbors are Station 1 and Station 5, and one of them is selected to transmit data depending on the direction. Only the token holder (the station having the token) can transmit frames in the network. IEEE 802.4 is more complex than the IEEE 802.3 protocol.
- Preamble (1 byte) is used for synchronization.
- Start delimiter (1 byte) is the field used to mark the beginning of the frame.
- Frame control (1 byte) verifies whether this frame is a control frame or a data frame.
- Destination address (2-6 bytes) specifies the address of the destination station.
- Source address (2-6 bytes) specifies the address of the source station.
- Payload (0-8182 bytes) is a field of the variable length to carry the useful data from the network layer. 8182 bytes is the maximum value if the 2-byte address is used. If the address length is 6 bytes, then the maximum size of the payload field is 8174 bytes, accordingly.
- Checksum (4 bytes) is used for error detection.
- End delimiter (1 byte) marks the end of the frame.
The bus network topology is not recommended for networks when transferring a large amount of traffic. Taking into account that the bus network topology with coaxial cables was used in the 1990s, and the maximum speed is 10 Mbit/s, you should not use this topology to build your network nowadays.
Ring Network Topology
The ring network topology is a modification of the bus topology. In the ring network topology, each station is connected to two other stations on either side. The two other stations are neighbors of this station. Data travels sequentially in one direction, hence, the network works in half-duplex mode. There are no terminators, and the last station is connected to the first station in the ring. The ring topology is faster than the bus topology. The coaxial cable and connectors used to install a network of the ring topology are the same as those used for the bus network topology.
If you build a large network using the ring topology, use repeaters to prevent data loss when transferring data over the network between stations on long cable fragments. Generally, each station works as a repeater and amplifies the signal. After data is transmitted, the data travels along the ring and passes intermediate nodes until this data is received by the destination device.
You can have higher latency if the number of stations connected to the network is high. For example, if there are 100 computers in the network, and the first computer sends a packet to the 100th computer in the ring, the packet has to pass through 99 stations to reach the target computer. Remember that data is transferred sequentially. All nodes must remain active to transmit data, and for this reason, the ring topology is classified as an active network topology. The risk of packet collisions is reduced because only one node in the network can send packets at a time. This approach allows equal bandwidth for each node in the network.
Token ring
The token ring network is the implementation of the IEEE 802.5 standard. This topology works by using the token-based system. Token ring is the technology introduced in 1984 by IBM. The token is the marker that travels over the loop in one direction. Only the node that has the token can transmit data.
The first station that starts to work in the network becomes the monitoring station or the active monitor, controls the network state, and removes floating frames from the ring. Otherwise, continuously floating frames circulate in the ring for an unlimited time. The active monitor is also used to avoid lost tokens (by generating a new token) and to clock errors.
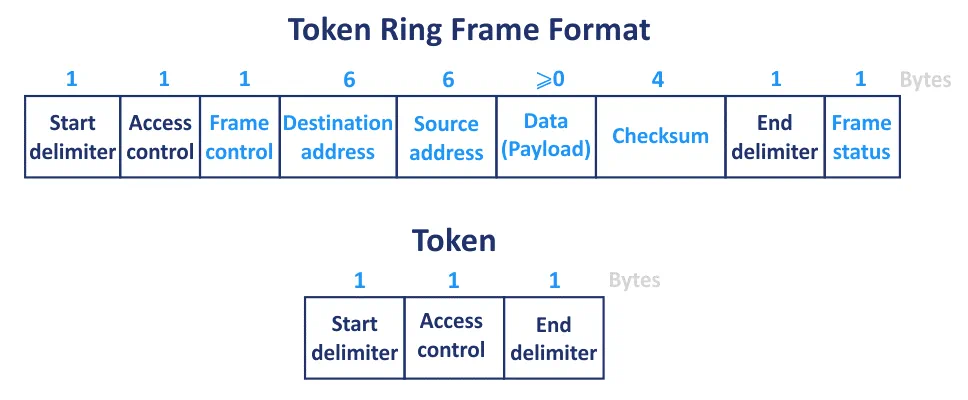
The IEEE 802.5 frame format for a token ring network is displayed on the diagram below.
- Start delimiter (1 byte) is used for synchronization and for notification of a station that a token is arriving.
- Access control (1 byte) is the field that contains the token bit, monitor bit, and priority bits.
- Frame control (1 byte)
- Destination address (6 bytes) – defines a MAC address of the destination device.
- Source address (6 bytes) – defines a MAC address of the sender.
- Payload (0 bytes or more) is the useful data (IP packet) that is transferred in a frame, and the size of the payload can vary from 0 to maximum token holding time.
- Checksum (4 bytes), which is also called frame check sequence or CRC (cyclic redundancy check), is used to check errors in the frame. Corrupted frames are discarded.
- The end delimiter (1 byte) marks the end of the frame.
- Frame status (1 byte) is a field used to terminate a data frame and serves as the ACK. This field can be set by a receiver and indicates whether the MAC address was recognized and the frame was copied.
The difficulty of the ring topology installation is medium. If you want to add or remove a network device, you need to change only two links. The ring topology is not expensive to install. But the list of advantages ends here.
Now let’s highlight the disadvantages of the ring network topology. Each fragment of the network can be a point of failure. A failure can be caused by a broken cable, damaged network adapter of a computer, cable disconnect, etc. In the case of link failure, the entire network fails because a signal cannot travel forward and pass the point of failure. Failure of one station causes failure of the entire network. All the data travels around the ring by passing all the nodes until reaching the destination node. Troubleshooting is difficult.
All nodes in the network of the ring topology share bandwidth. As a result, when adding more nodes into the ring, communication delays and network performance degradation occur. To reconfigure the network or to add/remove nodes, the network must be disconnected and stay offline. Network downtime is not convenient and cost-effective for an organization. Thus the ring network topology is not the best choice to build a scalable and reliable network.
The ring network topology in local area networks was popular in the 1990s until the beginning of the mass usage of the Ethernet standard with twisted-pair cables and more progressive star topology. Nowadays, the ring topology is not used and is not recommended for home and office usage due to the low network speed of 4 or 16 Mbit/s and the other disadvantages mentioned above.
The dual ring
The dual ring is a modified version of the ring topology. Adding a second connection between nodes in a ring allows the transfer of data in both directions and makes the network work in a full-duplex mode. Data is sent in clockwise and counter-clockwise directions in the network. If a link in the first ring fails, the second ring can be used as a link backup to continue network operation until the issue in the first ring is fixed.
The optical ring in modern networks uses the ring network topology. This network topology is primarily used by internet service providers (ISP) and managed service providers (MSP) to create connections in wide area networks.
Technologies and standards used to create an optical fiber ring:
- Resilient Packet Ring (RPR) that is known as IEEE 802.17
- STP (Spanning Tree Protocol) to avoid loops in the network
- Multiple section shared protection ring (MS-SPRing/4, MS-SPRing/2, etc.)
- Subnetwork connection protection (SNCP)
- Four-fiber bidirectional line-switched rings (BLSR/4), BLSR/2, etc.
- Synchronous transport module (STM-4, STM-16, STM-64, etc.)
- Synchronous Optical Networking (SONET) and Synchronous Digital Hierarchy (SDH)
Professional network equipment, such as switches, that support the appropriate standards are used to create a fiber ring. The price for this hardware is high. The optical ring with high availability is used to connect nodes in different districts of a city or in different cities to the high available and high-speed circle.
Star Network Topology
The star topology is the most common network topology used nowadays for the many advantages it provides. This topology requires a centralized unit, which is called a switch, and all other network devices are connected to this switch with own network cable. A switch has multiple ports (usually 4, 5, 8, 16, 24, 48, etc.), and all needed stations are connected to the switch to interact with each other in the network. There are no direct physical connections between the two stations in this case. If two stations interact with each other in the network, a frame leaves the network adapter of the sender and is sent to the switch, and then a switch retranslates the frame to the network card of the destination station.
The star network topology is easy to scale. If there are no free ports in a switch, change the switch to one with more ports or connect a second switch to the existing switch with a patch cord to expand the network of the star topology. Note that when the network is highly loaded, this connection between switches is a bottleneck because the data transfer rate between stations connected to different switches can be less than the data transfer rate between stations connected to ports of the same switch when. If you need to add a station to the network, take a patch cord, insert one end into the network adapter of the endpoint device and another end into the switch.
If any of the stations connected to a switch fails, the network continues to work without interruption. If a switch goes offline, the network cannot operate. Full-duplex and half-duplex modes are supported in the star network topology. This topology is easy in terms of maintenance.
Avoid loops when connecting network devices. If more than two connections are present between two network devices working on the second layer, a loop is created. For example, if you connect two switches by using two patch cords or insert a patch cord into two ports of one switch, you get a loop. The loop leads to communication disruptions within the network and broadcast storms that continue until you eject the unneeded network cable and power off the switch. If you want to create redundant connections, use devices with multiple network adapters that support NIC teaming or link aggregation.
Hub vs switch: What is the difference?
Both hub and switch are used to connect multiple devices in a local area network (LAN) that uses the star topology. When a signal that encodes a frame arrives at one port of a hub (a sender station that is connected to this port with a cable), the signal is sent to all ports of the hub and, thereby, to all devices connected to the hub. Only the station whose network card has the MAC address that is defined as the destination MAC address in the frame can receive the frame. All other network devices connected to the hub that are not destination devices and whose network adapters have other MAC addresses detect the sent signals and reject this frame. The disadvantage of the hub is that the network is overloaded. Instead of sending a frame from the hub to a destination network card, the frame is sent to all devices connected to ports of the hub. The network flooding reduces the bandwidth of the network. A hub operates on the first layer of the OSI model (a physical layer).
A switch is a more intelligent device. A switch remembers MAC addresses of connected devices and adds MAC addresses of devices connected to each port of the switch to the MAC address table. When a sender sends a frame to a target device, the frame is sent to the switch. The switch reads the MAC address of the network card of a destination station and checks the internal MAC address table to identify to which port of the switch the destination device is connected. Then, the switch sends the frame only to the port associated with the MAC address of the target device. There is no flooding and network overload. This approach ensures high network performance. There are no collisions when using a switch in a star network topology. A switch operates on the second layer of the OSI model (the data link layer). See the table below to see all OSI layers.
The Open System Interconnection Model (OSI)
| Layer number | Layer name | Protocol Data Unit (PDU) | Examples of protocols and standards |
| 7 | Application | Data received or transmitted by an application | HTTP, FTP, POP3, SMTP |
| 6 | Presentation | Data formatted for presentation | SSL, TLS |
| 5 | Session | Data passed to the network connection | NetBIOS, SAP |
| 4 | Transport | TCP segments, UDP datagrams | TCP, UDP |
| 3 | Network | Packets | IPv4, IPv6 |
| 2 | Data Link | Frames | Ethernet, PPP, STP, Token Ring |
| 1 | Physical | Bits | 100BaseTX, RS232, ISDN |
A switch is more secure than a hub. Since 2011, using hubs to connect network elements is deprecated by IEEE 802.3, the set of standards and protocols for Ethernet networks.
Note: Switches, hubs, routers, modems, and Wi-Fi access points belong to active network equipment. Active equipment has electronic circuits and needs electric power for operation. Cables, connectors, transceivers, patch panels, rack mounts, and Wi-Fi antennas are passive network equipment that don’t need electricity. Passive network equipment are used to connect active network equipment.
Star topology in the real life
Let’s look in detail at how traditional Ethernet networks use the star network topology and how the IEEE 802.3 standard works. Twisted pair cables (4×2 wires) are the most common. They are usually used for these networks, and ends of cables are crimped with RJ-45 connectors (that are also known as 8P8C – 8 Position 8 Contact). Both ends of the cable are crimped by using the EIA/TIA 568B standard. You can also crimp both ends of a cable by using EIA/TIA 568A because the working principle remains the same, but this practice is not common. Find more information about cables in the Types of Cables section at the end of this blog post.
Ethernet Standards
10BASE-T is the first implementation of Ethernet and uses a twisted pair cable (T in the name means the Twisted pair, BASE means baseband signaling). The maximum speed of the network is 10 Mbit/s. The required cable is UTP Cat.3 or higher (only orange and green pairs are used).
100BASE-TX, which is known as Fast Ethernet, was implemented in 1995 (IEEE 802.3u). This standard provides the speed of 100 Mbit/s in the network and requires the UTP Cat 5 cable.
1000BASE-T is known as Gigabit Ethernet (GbE or 1 GigE) and was described in the IEEE 802.3ab standard (that was ratified in 1999). The maximum data transfer rate is 1000 Mbit/s (1 Gbit/s). The required cable is UTP Cat 5e.
2.5GBASE-T is the standard referred to as IEEE 802.3bz, and the maximum data transfer speed is 2.5 Gbit/s. The IEEE 802.3bz standard was approved in 2016. The UTP Cat 5e cable is required.
5GBASE-T is similar to 2.5GBASE-T but provides a data transfer rate of 5 Gbit/s and requires the higher class of a cable – UTP Cat 6.
10GBASE-T is the fastest Ethernet standard that uses cables with copper wires with a maximum speed of 10 Gbit/s. The required cable is UTP Cat 6A. The IEEE 802.3an standard contains specifications for using a twisted pair for 10 Gbit/s connections.
RJ-45 connectors are used for cables in the previous Ethernet standards.
The maximum length of cable between the ports of two network devices is 100 meters for each standard mentioned above if twisted-pair cable requirements are met. If you need to connect two network devices that are 200 meters apart, use two 100-m segments of cable and connect them to a switch installed in the middle at 100 m from each device.
To achieve the highest speed for each standard, you must meet the minimum requirements: use the cable of the appropriate category, a switch that supports the needed mode, and network cards of devices connected to the switch. For example, if you want your devices in the network to operate at 1 Gbit/s speed, you must install 1-Gbit network cards on these devices, connect them to a 1-Gbit switch, and use the UTP Cat 5e cable that is crimped with RJ-45 connectors as a patch cord using the EIA/TIA 568B standard. When all connected devices work at a speed of 1 Gb/s, they work only in full-duplex mode.
Auto-negotiation is a feature used to determine the optimal network speed and data transferring mode (full-duplex or half-duplex) for a port linked to the port of another connected device. Auto-negotiation automatically determines the configuration of a port that is connected to the other end of the cable and sets the data transfer rate based on the lower value. If you connect a 100-Mbit network card to a 1-Gbit switch with a patch cord (Cat 5e), then the speed of the network connection is 100 Mbit/s. The backward compatibility with previous lower-speed Ethernet standards is a useful feature.
Frame format
The length of a standard Ethernet IEEE 802.3 frame is 1518 bytes, and the standard MTU (maximum transmission unit) is 1500 bytes. If you need stations in the network to exchange large amounts of data, configure them to use jumbo frames that allow frames to use the MTU of 9000 bytes. Jumbo frames can help improve performance when transferring data because the ratio of useful information and service information in the frames is higher. Not all devices support jumbo frames.
Another advantage of using the star network topology is that Ethernet networks using this physical network topology type support VLAN tagging. VLAN tags are used to divide a physical network into logical networks by using the same physical infrastructure. Logical networks are separated on the second layer of the OSI model by using VLAN tags written into the frames. Hardware must support VLAN tagging to use this feature. VLAN ID can range from 0 to 4094. 4094 is the maximum number of VLAN networks in one physical network.
Let me cover frame formats for IEEE 802.3 Ethernet networks that use the star network topology.
- Preamble (7 bytes) indicates the start of the frame and is used for synchronization between a sender and receiver.
- Start of frame delimiter (1 byte) is the field that is always set to 10101011. SFD (start of frame delimiter) marks the end of the preamble and start of the Ethernet frame, preparing for upcoming bits of the destination address. This field is the last chance for the network device(s) to synchronize.
- Destination address (6 bytes) contains the MAC address of a destination network card (for example, E8:04:62:A0:B1:FF). The destination address can be unicast, multicast, broadcast (FF:FF:FF:FF:FF:FF).
- Source address (6 bytes) contains the MAC address of the source network card of the sender device. The source address is always unicast.
- Type (Ethernet type) or length (2 bytes) defines the length of the Ethernet frame. The type field indicates the layer 3 (L3) protocol (0x0800 – IPv4, 0x86DD – IPv6), whether the frame is using 802.1q VLAN tagging (0x8100), etc.
- Data payload (maximum 1500 bytes for standard frames or 9000 bytes for jumbo frames) is an encapsulated L3 packet that is carried by a frame. A packet is a typical PDU (protocol data unit) for the third layer of the OSI model (the Network layer).
- Checksum, FSC or CRC (4 bytes) is used to verify frame integrity. CRC is calculated by the sender, then a recipient receives the frame, calculates this value and compares with the received CRC value in the frame.
A 14-byte header of an Ethernet frame contains the destination address, source address, and type (length). If VLAN tagging is used, an additional 4-byte VLAN tagging field is added to a frame after the source address field.
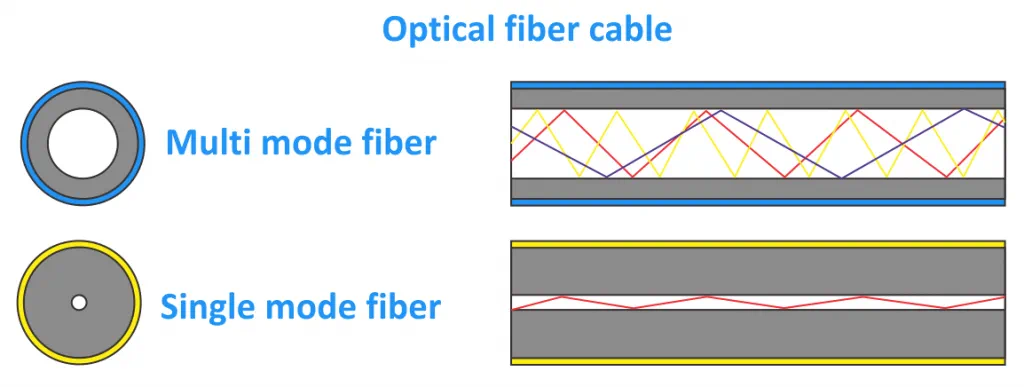
Optical connection
The star network topology is also used to build networks based on optical cables (optical fiber) if you need to have longer cable segments or lower latency. 10GBASE-S and 10GBASE-E are modern standards for 10 Gbit/s networks using optical fiber to establish connections. A switch with transceivers and SFP connectors is required in this case to build a star topology network.
SR (short reach) transceivers are used for a distance of up to 300 meters.
LR (long reach) transceivers support cable length in the range of 300 m–3 km.
ER (extended reach) transceivers support cable length from 30 km to 40 km.
The multimode (MM) optical cable is used for short distances (less than 300 m).
The single-mode (SM) optical cable is used for long distances (more than 300 m).
There are transceivers that allow you to connect copper Cat 6A cables with RJ-45 connectors to SFP+ ports for maximum compatibility. The optical cable is connected to transceivers by using LC connectors. Building a physical network using optical cables is more difficult than building a network using copper cables of Cat 6A.
Advantages of the star topology
The star network topology is outstanding. The star is the most common network topology type nowadays. Let’s summarize the advantages of this network topology type.
- One network card per station is enough
- Easy installation and maintenance
- Easy troubleshooting
- High reliability and compatibility
- Fast speed
- Support of twisted pair and optical cables
- Flexibility and scalability
Wi-Fi connection
If a wireless network connection is used by installing an access point at home or in the office, the wireless network usually uses the star network topology. The 802.11n (a/b/g/n) standard is used in this case. The Wi-Fi access point acts as a switch connected with wireless network adapters of stations and represents the star topology.
Tree Network Topology
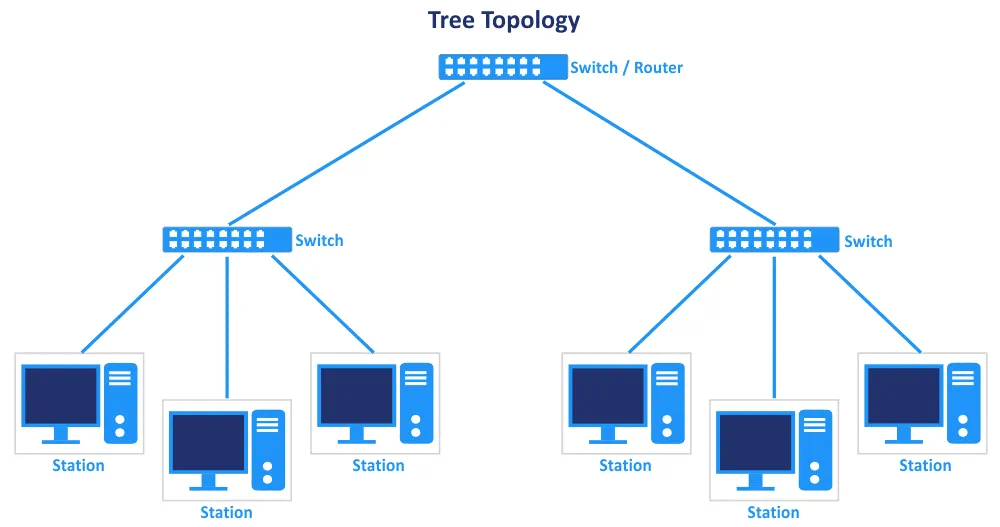
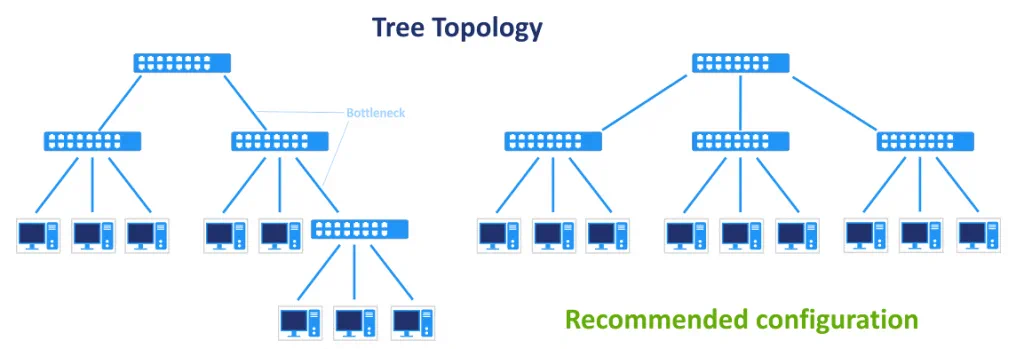
The tree network topology is an extension of the star topology and is widely used nowadays. The idea of the tree topology is that you can connect multiple stars like branches into a complex network by using connections between switches. Stations are connected to the ports of these switches. If one of the switches fails, the related segment of the network goes offline. If the main switch located on the top of the tree topology goes offline, network branches cannot connect to each other, but the computers of the branches continue to communicate with each other. Failure of any station connected to the network doesn’t affect the network branch or the entire network. The tree topology is reliable and easy to install, maintain, and troubleshoot, and provides high scalability. There is one connection between each node of the network when using this topology (see the network topology diagram below).
Protocols and standards applicable for the star network topology are used for the tree topology (including switches, cables, and connectors). Also, routers can be used to divide subnetworks from each other on the third level of the OSI model. As a result, network protocols of the third layer are used, and the appropriate configuration of network equipment is performed. The tree network topology is widely used in large organizations because it is easy to install and manage. The hierarchical network structure is present. Opt for connecting all switches of network branches to the main switch to avoid creating a long chain of switches that can cause bottlenecks and reduced network performance when data is transferred via segments between switches.
An example of network configuration
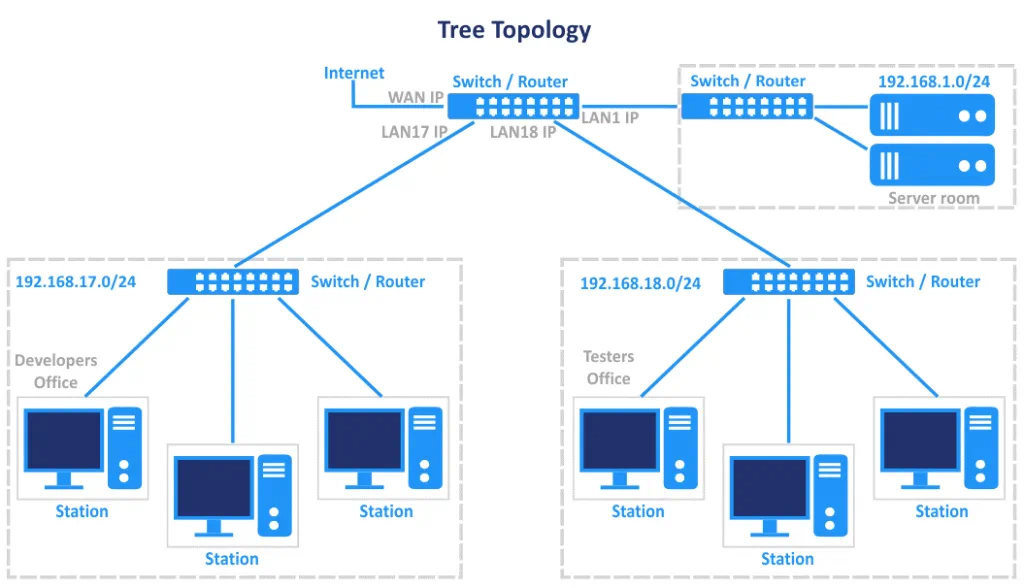
Let’s look at an example of the tree network topology and how this network topology type is used in practice. For example, there is an organization with multiple departments, and each department occupies one office in a building. Departments are located on different floors of the building. Installing a network by using a single star topology is not rational because this would lead to extra consumption of cable to connect all stations in different locations of the building to a single switch. Also, the number of stations can be higher than the number of ports in the switch. In this case, the most rational solution is to install a dedicated switch in the main office of each department, connect all the stations of each department to the appropriate switch, and connect all the switches of departments to the main switch located in the server room. The main switch is on the top of the tree hierarchy in this example. The main switch can be connected to a router to access the internet. If there is a department located in another building, and the distance to your switch in the main building is more than 100 meters, you can use an additional switch with a UTP cable. This switch divides the distance into segments that are under 100 meters. As an alternative, use the optical cable (and the appropriate converters or switches) to connect this remote office to the main switch.
To simplify administration and improve security, you can install routers for each department and create subnets for each department. For example, developers are in the 192.168.17.0/24 network, accountants are in the 192.168.18.0/24 network, testers are in the 192.168.19.0/24 network, servers are in the 192.168.1.0/24 network (the main subnetwork), etc.
What is a router?
A router is a device that operates on the third layer of the OSI model (the network layer) and operates with packets (the PDU is a packet). A router can analyze, receive, and forward packets between different IP networks (subnetworks) by using the IP addresses of source hosts and destination hosts. Invalid packets are dropped or rejected. Different techniques are used for routing, such as NAT (network address translation), routing tables, etc. The firewall and network security are additional features of the router. Routers can select the best route to transfer packets. A packet is encapsulated into a frame.
A router has at least two network interfaces (usually LAN and WAN). There are popular models of routers that are combined with a switch in a single device. These routers have one WAN port and multiple LAN ports (usually 4-8 for small office/home office models). Professional routers have multiple ports that are not defined as LAN or WAN ports, and you should configure them manually. You can use a physical Linux server with multiple network adapters and connect this machine as a router. Connect a switch to the LAN network interface of this Linux router to have the tree network topology type.
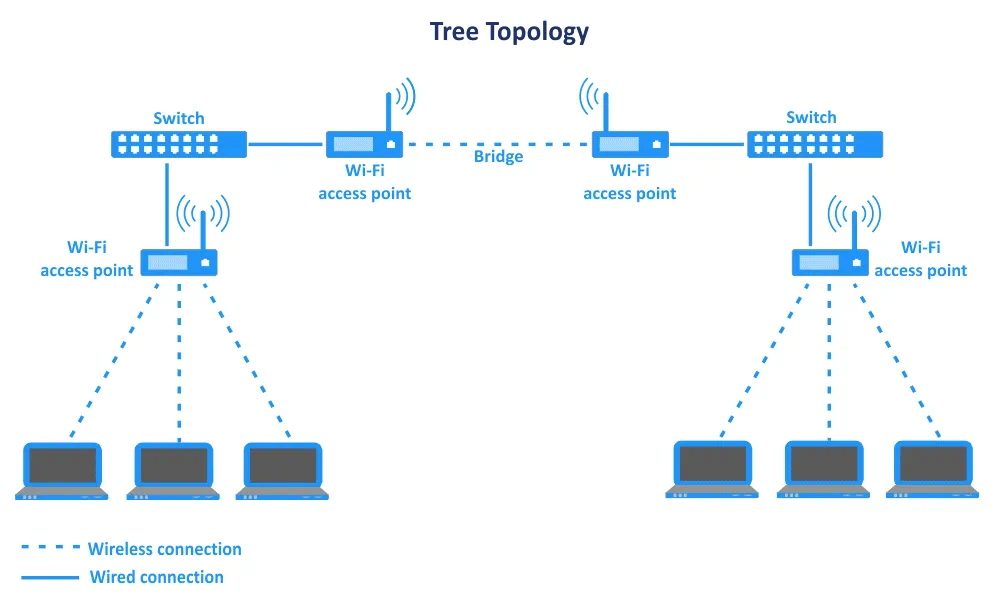
Wi-Fi connection
Just as for the star network topology, wireless network equipment can be used to create network segments of the tree topology in a mix with wired segments. Two identical Wi-Fi access points can work in the bridge mode to connect two segments of the network (two stars). This approach is useful when you need to connect to offices that are more than 100 meters apart and when it is not possible to install a cable between the offices. The following tree network topology diagram explains this case. A switch is connected to each Wi-Fi access point operating in the bridge mode, two other Wi-Fi access points are connected to the appropriate switch, and client stations are connected to these access points (forming branches of the tree that are networks of the star topology).
Mesh Network Topology
A mesh network topology is a configuration in which each station in the network is connected to the other stations. All devices are interconnected with each other. There are two types of mesh: a full mesh and a partial mesh. In a partially connected mesh, at least two stations of the network are connected to multiple other stations in the network. In a full mesh, each station is connected to all other stations. The number of connections for a full mesh is calculated with the formula Nc=N(N-1)/2 links, where N is the number of nodes in the network (for the full-duplex mode of communication). See the network topology diagram below.
The mesh network topology provides redundancy for a network but can be costly due to the high number of connections and total length of used cable. If one station fails, the network can continue operation by using other nodes and connections. If data was transferred via the failed node, the route is changed, and data is transmitted via other nodes.
Each node is a router that can create and modify routes dynamically to transfer data in the most rational way (dynamic routing protocols are used in this case). The number of hops can vary when changing the route between source and destination device. Routing tables consist of destination identifier, source identifier, metrics, time to live, and broadcast identifier. Routing works at the third layer of the OSI model. Sometimes flooding techniques are used instead of routing. This type of network topologies can be used for the transmission of high amounts of traffic thanks to connection redundancy.
It is difficult to add a new station to the network because you need to connect a new station to multiple other stations. Adding or removing nodes doesn’t interrupt the operation of the whole network. Multiple network cards per station are required to establish all needed connections. After adding a new station, you may need to install additional network cards on other stations that must be connected to the new station. The mesh network topology is scalable, but this process is not straightforward. Administration can be time-consuming. The fault-tolerant topology ensures high reliability. There are no hierarchical relationships.
The mesh network topology is an example of connecting multiple sites on the internet. This network topology is widely used for WAN (wide area network) connections, for networks of mission-critical organizations such as military organizations, etc.
Wi-Fi connection
The mesh network topology in Wi-Fi networks is used to extend the coverage of wireless networks that are called wireless mesh networks. The infrastructure mesh architecture is the most common for this type of network topologies. Wireless technologies used to create this network topology type are Zigbee and Z-Wave that are based on the IEEE 802.15.4 protocol, WirelessHART. IEEE 802.11, 802.15, and 802.16. Cellular networks also can work using the mesh network topology.
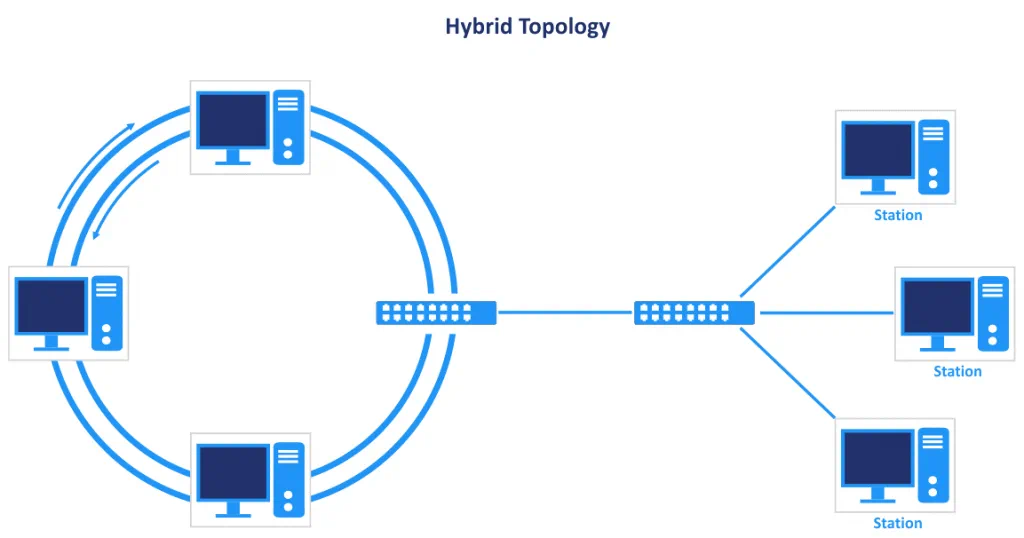
Hybrid Network Topology
The hybrid topology combines two or more of the network topology types covered earlier. A combination of the star and ring types of network topology is an example of a hybrid network topology. Sometimes you might need the flexibility of two topologies in your network. The hybrid topology is usually scalable and has the advantages of all child topologies. The disadvantages of the topologies are also combined, making installation and maintenance difficult. The hybrid topology adds more complexity to your network and may require additional costs.
The star-ring topology is one of the examples of the hybrid type of network topologies that you can find nowadays. When talking about the ring part, we don’t mean coaxial cables with T-connectors and BNC connectors. In a modern network, a fiber ring is used to connect nodes at long distances. This hybrid network topology (ring + star) is used to build networks between different buildings located far away within one city or in different cities. Using the star topology when the distance between nodes is high is difficult and causes overconsumption of cable.
The advantage of the fiber ring with multiple lines is the absence of a single point of failure. Redundant optical links provide high availability and reliability. In case of one optical link corruption, reserve channels are used. Different fiber lines between nodes of the circle can be traced by using different geographical routes.
Fiber switches/routers that are nodes of the ring are connected to switches/routers that are parts of network segments using the star network topology. That connection has advantages for building local area networks. Fiber media converters are used to connect switches/routers compatible with fiber cables and related connectors to switches/routers compatible with copper cables crimped with the appropriate connectors if a ring and star use different types of cables and network equipment.
Types of Cables
Cables are important components of physical network topology. Network speed and overall costs for network installation depend on the selected network topology, cables, and other network equipment. Different types of cables have been mentioned in the blog post when giving real examples of using different types of network topology. Let’s look at the most used cables for different types of network topology explained in this blog post for a better understanding of physical topologies.
Coaxial cable
The coaxial cable consists of a central copper wire as the inner conductor. Solid copper or several thin strands of copper can be used for the central conductor in different cable models. This inner conductor is surrounded by an insulating layer protecting the core wire. The insulating layer is surrounded by conductive aluminum tape and weaved copper shield. The external layer is polymer isolation, which is black or white.
RG-58 is a popular version of coaxial cable and has an impedance of 50 Ohm. This cable is also referred to as 10Base2 Thinnet cable. RG in the name stands for “radio guide.” Other examples of coaxial cable are RG-6, RG-8, RG-59. Nowadays, coaxial cables are used to connect Wi-Fi antennas to the appropriate network equipment (5D-FB, 8D-FB, LMR-400 cable types).
Twisted pair
Twisted pair cables are widely used for networks due to simplicity of usage, high bandwidth, and affordable price. Two separate insulated copper wires (about 1mm in diameter) are twisted together to form a pair. One to four pairs are used in different cable types and categories. The reason for twisting is to reduce noise signals. Twisted pairs are covered with an external insulated shield that protects a cable against mechanical damage. There are three main types of twisted pair cables: UTP, FTP, and STP.
UTP (Unshielded Twisted Pair) is a cable that comprises of wires and insulators.
FTP (Foil screened Twisted Pair) or F/UTP is a cable in which all twisted pairs together are covered with a metal shield (aluminum foil). An additional single wire less than 1 mm in diameter is included inside the cable. As a result, FTP cables support grounding if the appropriate connectors are used. Individual twisted pairs are unscreened.
STP (Shielded Twisted Pair) contains a weaved metal shield around twisted pairs. Each twisted pair is shielded with aluminum foil. The whole cable is hard and is more difficult to twist (the cable is not as highly flexible as FTP and UTP). The STP cable provides better protection against electromagnetic noise and mechanical damage.
Category 5e or higher is used nowadays to install networks. The higher the category is, the higher data transfer rate is (100MHz, 250 MHz, 500 MHz), and data transferring speed is supported. You can use an FTP or STP cable of the same category instead of a UTP cable. UTP Cat.3 has only two twisted pairs. UTP Cat.5 and higher have 4 twisted pairs. Cable crimping is easy and can be done by anyone who has a cable crimping tool.
Optical fiber cable
Optical fiber cable provides the lowest latency and covers the longer distance with one cable segment (without repeaters). Fiber optic cable is thin and consists of two layers of glass. The core glass layer is a pure glass that is a waveguide for light signals for a long distance. The cladding is a glass layer surrounding the core and has a lower index of refraction compared to the core. The technology is based on the total internal reflection principle.
Single-mode fiber (SMF) cables and multimode fiber (MMF) cables are used. The MMF cables have a bigger diameter and are used to propagate multiple light rays (or modes), but they are better for short distances. MMF cables usually have a blue color. The SMF cables are better for long distances and are yellow. Popular connectors are SC, FC, LC, and ST.
The price for fiber optic cables is high. Welding of optical fiber is difficult comparing to the wiring of twisted pair cables or coaxial cables. The price of transceivers needed to plug an optical cable into a switch or router adds expenses. The ends of optical fibers should always be clean as even a piece of dust can cause significant issues.
Conclusion
This blog post has covered network topologies, including physical topologies, logical topologies, and examples of using them in real life. If you need to build a local area network, use the star topology, which is the most common network topology today, or the tree network topology, which is a highly scalable modification of the star topology. The ring and mesh topologies are mostly used by internet service providers, managed service providers, in data centers. These are more difficult to configure. The variety of network topology types, network equipment, standards, and protocols allow you to install a network of any configuration in your environment depending on your needs.
When you have installed a network and connected servers and a virtual machine to the network, don’t forget to configure data backup and protect your data. NAKIVO Backup & Replication is a universal data protection solution that supports backup of Linux machines, Windows machines, VMware virtual machines (VMs), Hyper-V VMs, Oracle Databases, and Office 365 via a network. Download the Free Edition of NAKIVO Backup & Replication and try the product in your environment.