Microsoft Office 365 Malware Protection: A Short Guide
Malware is spreading across the world and infects many computers every day. Malware can cause data corruption and data loss that reflects negatively on a particular user and the entire company. Hackers use sophisticated techniques and complex algorithms to implement identity theft and malware attacks.
If you use virtual machines in the cloud, they can also be at risk. That’s why you should protect all machines against malware. There are different ways that malware infects computers including distributing malicious files on shared storage, email attachments, harmful links, and so on. This blog post explains how you can protect against malware when using Microsoft Office 365 backup and covers Microsoft Office 365 malware protection.
Main Categories of Malware
First of all, let’s find out what is malware and what are the known types of malware. Understanding this helps to define a malware protection strategy.
Viruses are a classic form of malware. A virus is the program that infects files to spread and infect other files and computers. The infected files used by programs or executable infected files are used to spread a virus. A virus can be a piece of malicious code that can be attached to the appropriate file types, for example, macros in a DOC file can contain malicious code and infect other files and computers. A computer worm is a type of a computer virus that uses software vulnerabilities to spread across a network and infect files on other computers. For example, Stuxnet is one of the most well known computer worms that can target a nuclear power plant to prevent producing nuclear weapons.
If you notice that your computer is working slowly, some system files of your operating system are missing, errors are displayed, or some components are missing in the graphical user interface of the operating system, you should check your computer for viruses.
Spyware is another type of malware used to steal data from computers. Spyware is unwanted software that can collect/steal entered passwords, security keys, visited sites, personal data, and stored files. Spyware can contain a keylogger. Then the stolen data can be sold to advertising companies or can be used to compromise accounts from different computers, sites or services. Cybercrime attackers can steal data about credit cards and bank accounts used for payment via internet to steal money from their victims. Spyware is often hard to identify because it is developed to be invisible.
Spyware can be divided into four types:
- Adware
- Trojan
- Tracking cookies
- System monitor
Ransomware is probably the most dangerous type of malware. When a computer is infected with ransomware, ransomware starts to encrypt targeted types of files (for example, JPG, DOC, XLS, MOV, AVI, VMDK, VHD, VDI) with a long encryption key. The encrypted files are corrupted files that cannot be repaired in most cases. After encrypting files, ransomware demands that a user pay money for decrypting files within a limited period of time. However, in most cases, retrieving files is impossible as they cannot be repaired/decrypted even after paying money. Finding the decryption key is almost impossible. For example, the time needed to crack a 128-bit key takes 500 billion years with the current performance level of computers. Thus, encrypted files are irreversibly corrupted files in this case.
Encryption of files is a legal feature that is built in modern operating systems and that’s why antiviruses cannot detect ransomware in all cases. Some light versions of ransomware can lock an operation system by modifying system files and configuration without damaging other files on disks. However, nowadays this type of ransomware is the exception rather than the rule. When files are corrupted by ransomware, the probability of restoring files is extremely low. The most effective methods to avoid data loss are preventive measures. It is recommended that you predefine a malware protection strategy.
How to Prevent Malware Infection
General recommendations to prevent malware infection:
- Don’t download files from untrusted and suspicious sources
- Don’t click pop-up messages
- Don’t open email attachments from unknown senders
- Install critical security patches for installed software
- Use strong passwords
- Keep certificates in a safe location
- Back up your data
As for Microsoft Office 365 malware protection, in addition to the recommendations above, you can use two approaches that complement each other:
- Use Microsoft Office 365 Advanced Threat Protection and related features for malware protection
- Perform Microsoft Office 365 backup
Malware Protection in Microsoft Office 365
Users who are considering using Microsoft Office 365 usually ask:
- Does Microsoft Office 365 include virus protection?
- Does Microsoft Office 365 include Exchange Online Protection?
- Is Microsoft Office 365 ransomware safe?
The answer is “Yes”. Read the information below to learn more.
Malware protection in Microsoft Office 365 is provided by three main components, which are integrated with each other:
- Microsoft Office 365 Advanced Threat Protection
- Microsoft Office 365 Exchange Online Protection
- Microsoft Office 365 Threat Intelligence
These main Microsoft Office 365 components contain many smaller features that can protect Microsoft Office 365 users against threats. These threats include the most popular ways of malware infection such as malicious links or attachments in email messages sent from spoofed sender addresses, emails with infected attachments, and emails containing scripts or written by using social engineering techniques. Distributing malware via email is one of the most popular methods of infecting victims.
Now that you know the main types of malware, methods of infection and malware spreading, let’s look at how you can use Microsoft native components and features for Microsoft Office 365 malware protection.
Configuration of Malware Protection in Microsoft Office 365
Let’s look at how to configure malware protection in Microsoft Office 365 by using the web interface.
- Open Microsoft Office 365 Security & Compliance admin center by using the link:
https://protection.office.com/
You can also access Microsoft Office 365 Security & Compliance page from the Microsoft 365 admin center. - In the left pane, click
Threat managementand then clickPolicies. Anti-malware policies are used to control the settings of malware detection and their notifications options. - On the
Policypage clickAnti-malware.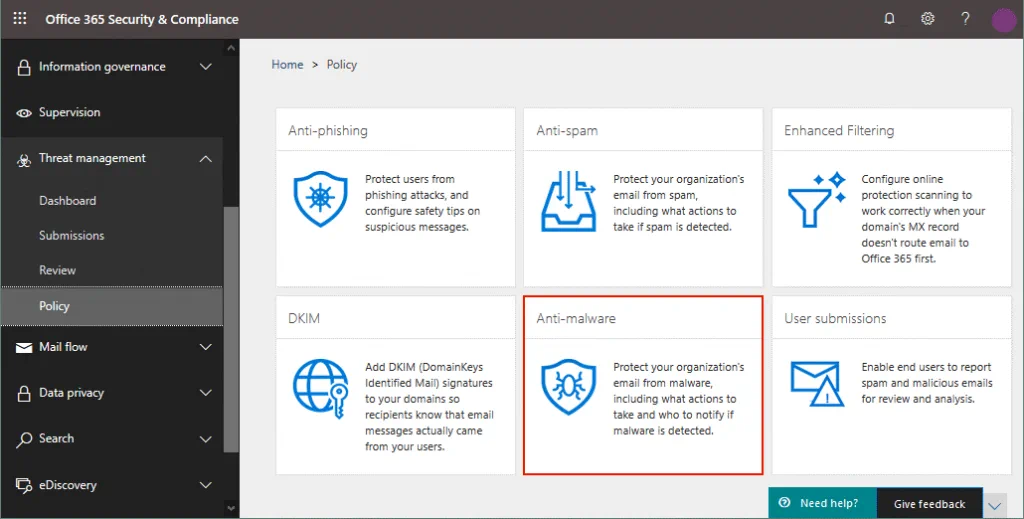 Now you are in the malware protection center for Microsoft Office 365.
Now you are in the malware protection center for Microsoft Office 365. - You can see the default policy that can be viewed and edited by administrators but it cannot be deleted. Let’s create a new policy.
- Click the
+icon to create a new anti-malware policy.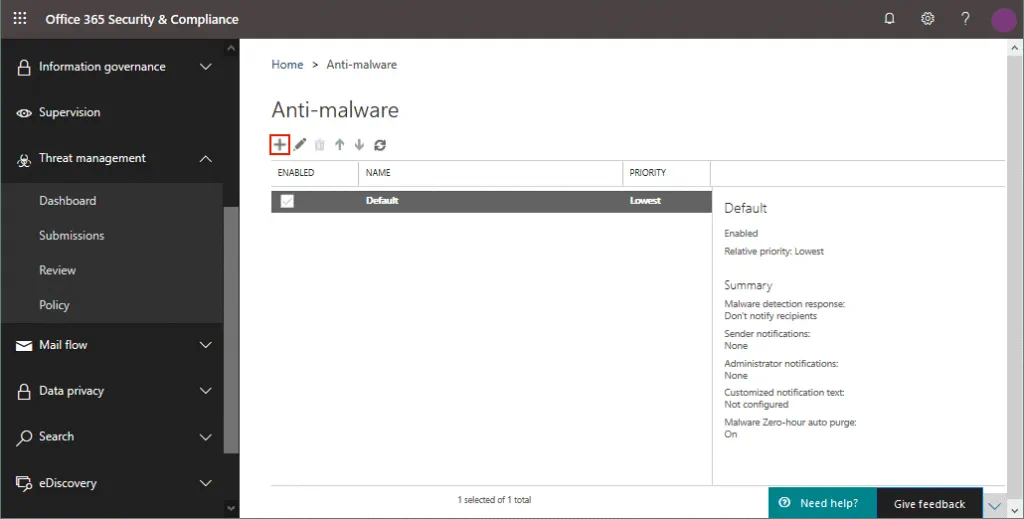
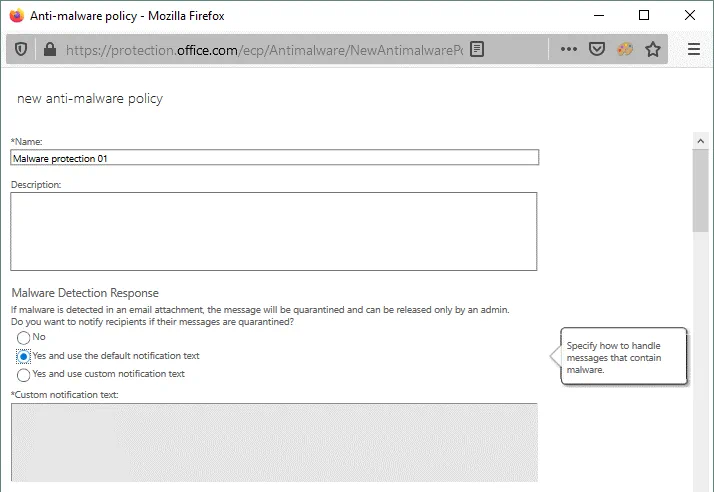
- A new window opens. You should enter a policy name and description. Settings are grouped in multiple sections.
Malware Detection Response
The malware detection response option allows you to notify recipients if malware is detected in email attachments. By default, this option is turned off and recipients are not notified automatically when malware is detected and the email message is moved to quarantine. You can enable automatic recipient notifications by using one of the suggested options:
- Yes, and use the default notification text
- Yes, and use custom notification text
If you enable notifications by using the first option with the default notification text, all attachments will be removed from a delivered email message. The removed attachments will be replaced with the Malware Alert Text.txt file that contains the following information:
Malware was detected in one or more attachments included with this email message.
Action: All attachments have been removed.
If you select to use custom notification text, your custom message will replace the default text in the Malware Alert Text.txt file attached to the email message instead of the quarantined or deleted malware files.
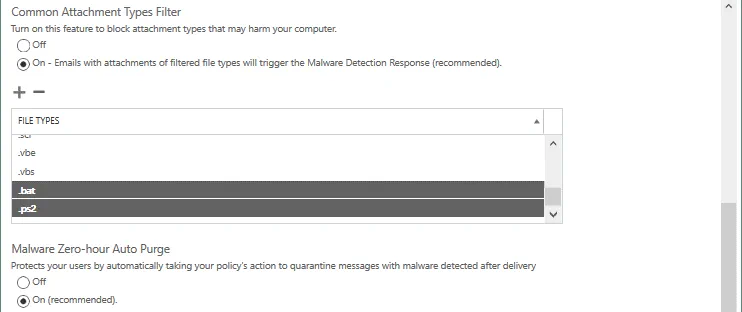
Common Attachment Types Filter
This filter allows you to block some file types with the appropriate extensions that can constitute a threat. It is recommended that you block executable file types such as EXE, BAT, COM, CMD, PS1, SH, RPM, JS, DMG, VBS, and others. Best effort true-typing is used when possible to detect the appropriate file types regardless of the extension of the file. By default, the Common Attachment Types Filter is disabled and you should turn it on manually by selecting the appropriate option (see the screenshot below).
Click the + icon to add file types that must be blocked when detected in email attachments.
By default, ACE, ANI, APP, DOCM, EXE, JAR, REG, SCR, VBE, and VBS are selected.
Malware Zero-Hour Auto Purge
Malware Zero-Hour Auto Purge (ZAP) moves malicious email messages after these messages have been delivered to Exchange Online mailboxes. This feature is turned on by default and it is recommended to leave this feature enabled for Microsoft Office 365 malware protection.
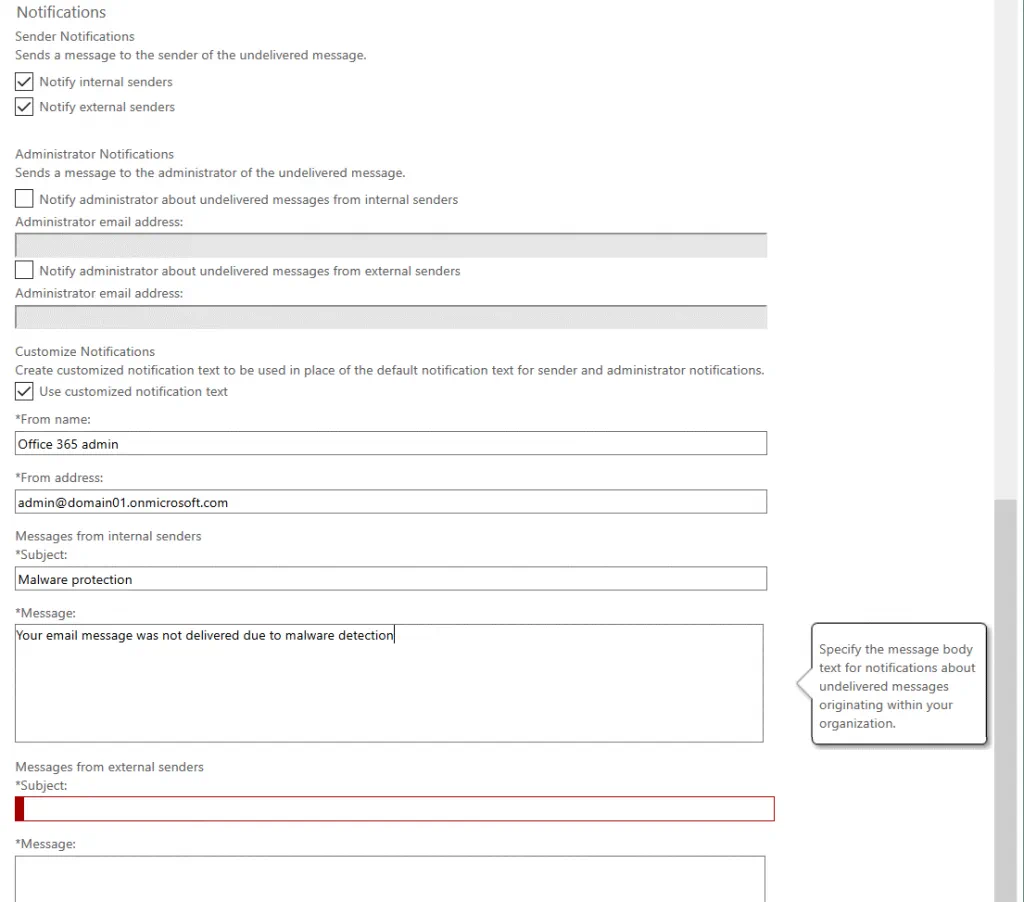
Notifications
Sender notifications allow you to notify a sender if a sent message is not delivered due to malware detection and moving the message to quarantine. By default, this option is disabled. In order to enable sender notifications, select the appropriate checkbox to notify internal senders and/or notify external senders (see the screenshot below). Internal senders are senders within your organization and external senders are the senders outside your organization who use another domain name.
The text of the default notification message contains the information:
From: Postmaster postmaster@yourdomain.com
Subject: Undeliverable message
This message was created automatically by mail delivery software. Your email message was not delivered to the intended recipients because malware was detected. All attachments were deleted.
You can also configure sending notifications to the administrator of the undelivered message from internal and external senders.
Customize notifications options allow you to set a name, email account, email subject, and text for notifications that must be set to internal and external senders.
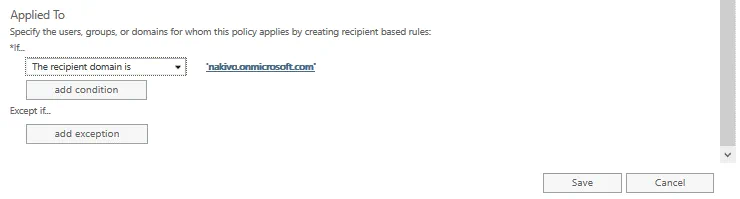
Applied to
Recipient Filters allow you to define recipient conditions and exceptions. They determine users for whom the policy is applied. You can specify users, groups, or domains by using the conditions:
- The recipient is (select one or more email accounts)
- The recipient domain is (select one or more domain)
- The recipient is a member of (you can select a group email account that contains multiple users)
Multiple conditions and exceptions can be set. The same conditions or exceptions use the OR logic and different conditions or exceptions use AND logic. For example:
domain1.comordomain2.comuser1@domain1.comand a member ofgroup1@domain2.com
Thus, in the If section click the drop-down menu and select the needed option, then click add condition. Click add condition once more to add the second condition.
After that in the Except if section click add condition and add the needed exception condition. You can add multiple exceptions to the anti-malware policy.
Hit Save to save settings and create a new anti-malware policy for malware protection in Microsoft Office 365.
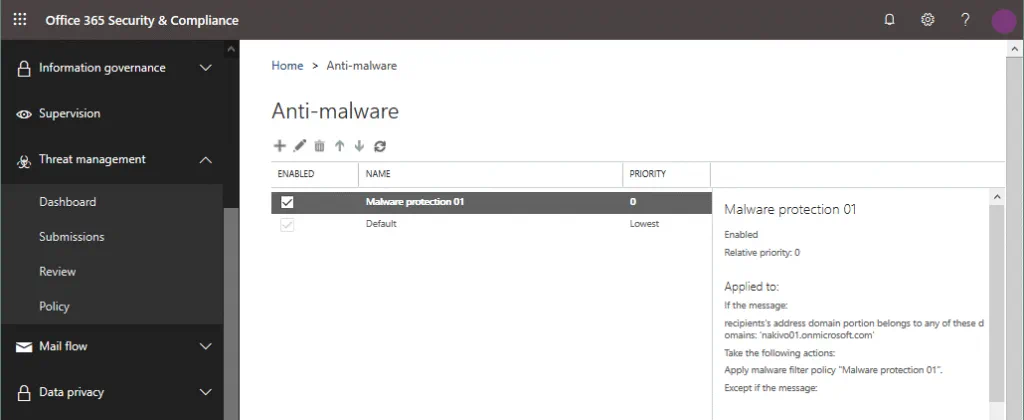
Now the created anti-malware policy is displayed in the policy list on the Anti-malware policy page. You can enable, disable, edit, and delete policies. If you want to disable a policy, you should unselect the checkbox near the policy name. If you want to move a policy up or down in the list to change the order (priority) of policies, you should click the policy and hit arrow icons in the web interface. Double click a policy name to edit the policy. A policy in the top of the list has the highest priority.
You can test your anti-malware policies configured for Microsoft Office 365 malware protection by sending a test email with a special attached file used to test antiviruses. Create the EICAR.TXT file and add the string to this file:
X5O!P%@AP[4PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*
This string must be the only string in the text file. The size of the file must be 68 bytes after saving. Save this file, create a new email message, attach the IECAR.TXT file, and send this message to a user in your domain used for Microsoft Office 365.
Microsoft Office 365 spam and malware protection should filter this email message and send a notification message according to your policy configuration and malware detection response settings (the entire message can be deleted or the attachment can be deleted).
Malware Protection Using a Backup Solution
One more preventive strategy to protect your data when using Microsoft Office 365 is to perform data backup.
Read our blog posts about OneDrive backup, SharePoint backup, and Exchange Online backup to learn more.
You can perform Microsoft Office 365 data backup in addition to using Microsoft Office 365 malware protection capabilities provided by Microsoft.
Conclusion
Protection against malware is important for every single user and the whole company. This blog post has covered general malware protection recommendations and explained how to use Microsoft Office 365 malware protection. Microsoft Office 365 protection includes three main components and many features. You should configure rules and policies in the web interface of the Microsoft Office 365 admin center according to your requirements and security policy. Microsoft also provides a service that can be used to send suspicious files for malware analysis.